Blog Posts
Keeper: A Simple Password Manager
- Siddharth Kumar
- Software
- 09 Oct, 2024
Managing multiple passwords can be overwhelming, but Keeper offers a simple solution. Keeper is a password manager that allows users to securely store, view, and manage their passwords. Built with th
Read More
The Reality of Student Life and Careers in Tier 3 Colleges vs. IITs and NITs
- Lokeshkumarcv
- Article , Student , Tier3colleges
- 05 Oct, 2024
In India, the competition to secure a seat in premier institutes like the Indian Institutes of Technology (IITs) and National Institutes of Technology (NITs) is intense. These institutions are often
Read MoreBuilding a Decentralized Cryptocurrency Exchange
- Chitesh MSV
- Project , Web development
- 26 Sep, 2024
Team: Clueless CodersTeam Members: Chitesh MSV, Priyanka Dhinakar, Sajietha K, Jayanth M Contact: mchitesh7@gmail.com |In today's rapidly evolving financial world, cryptocur
Read More
Understanding Deep Learning: A Journey into the Future of AI
- Akkupalli Deepak yadav
- Article , Python , Deep learning
- 20 Sep, 2024
Deep learning, a subset of machine learning, has revolutionized the field of artificial intelligence (AI) by enabling machines to learn from vast amounts of data and perform complex tasks with remark
Read More
Understand Bubble Sort Algorithm
- Diego Santos
- Software
- 18 Sep, 2024
Bubble Sort is a simple sorting algorithm that repeatedly steps through the list, compares adjacent elements, and swaps them if they are in the wrong order. This process continues until the list is s
Read More
Loan Eligibility Predective Analyser
- Sanjeevan S
- Project , Python , Software
- 15 Sep, 2024
Loan Eligibility Predictive Analytics: A Comprehensive Solution **This project offers an advanced machine learning solution for determining loan eligibility, leveraging powerful data prepr
Read More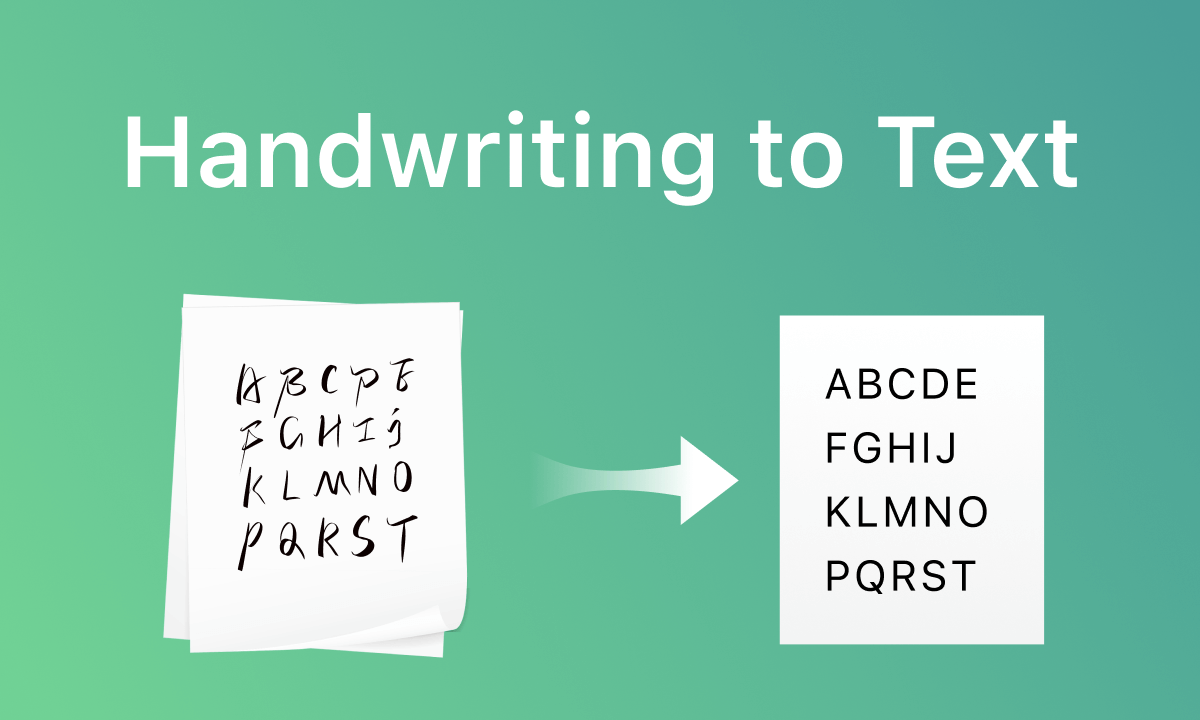
Building an Image-to-Text Converter with Handwritten Text Recognition
Introduction In the era of digitization, converting images to text has become a vital technology for various applications, including digitizing handwritten notes, automating form processing, and e
Read More
Startegies to detect frauds in credit cards payments online
- Adluru Umesh
- Research paper , Fraud detection , Sql
- 25 Apr, 2024
The document presents an in-depth exploration of the application of machine learning (ML) techniques in detecting fraud in credit card payments and anomalies in e-commerce transactions. The rapid grow
Read More
Understanding Ransomware and a Dive into Snakes Ransomware
- Krishna Chaitanya Ethamukkala
- Project , Ransomware , Python
- 16 May, 2022
What is Ransomware? Ransomware is a type of malicious software designed to block access to a computer system or encrypt its data until a sum of money, or ransom, is paid. It’s a form of cyber exto
Read More
How to build an Application with modern Technology
- John Doe
- Architecture
- 04 Apr, 2022
Nemo vel ad consectetur namut rutrum ex, venenatis sollicitudin urna. Aliquam erat volutpat. Integer eu ipsum sem. Ut bibendum lacus vestibulum maximus suscipit. Quisque vitae nibh iaculis neque blan
Read MoreCategories
- Article (3)
- Ai (3)
- Software development (3)
- Engineering (2)
- Ocr (1)
- Text extraction (1)
- Project (5)
- Web development (3)
- Javascript (1)
- Programming (2)
- Blockchain (2)
- Cryptocurrency (1)
- Fintech (1)
- Decentralized finance (1)
- Technology (3)
- Ar vr (1)
- blockchain (1)
- Cybersecurity (1)
- machine learning (1)
- artificial intelligence (1)
- networking (1)
- Ip addresses (1)
- Computer networks (1)
- Mern stack (1)
- Ai integration (1)
- Algorithms (1)
- Computer science (1)
- Cryptography (1)
- Python (4)
- Deep learning (1)
- Large language models (1)
- Natural language processing (1)
- Student (1)
- Tier3colleges (1)
- Image text converter (1)
- Software (4)
- Architecture (1)
- Quantum computing (1)
- Ransomware (1)
- Website (1)
- Research paper (1)
- Fraud detection (1)
- Sql (1)
Tags
- Ai engineer
- Software development
- Machine learning
- Artificial intelligence
- Python
- Javascript
- Arrays
- Programming tips
- Blockchain
- Cryptocurrency
- Bitcoin
- Ethereum
- Smart contracts
- Defi
- blockchain
- Cybersecurity
- networking
- Ip addresses
- Computer networks
- Network security
- Mern stack
- Ai web development
- Javascript frameworks
- Full stack development
- Time complexity
- Algorithms
- Big o notation
- Decentralization
- Cryptography
- Deep learning
- Llm
- Natural language processing
- Ai
- Student
- Tier3colleges
- Image to text
- Python3
- Kaggle
- Pandas
- Numpy
- Silicon
- Technology
- Data structures
- Ruby
- Quantum computing
- Developers
- Future of technology
- Software engineering
- Password manager
- Snakes ransomware
- Ransomware
- Html
- Css
- Java script
- Credit card frauds
- Fraud detection